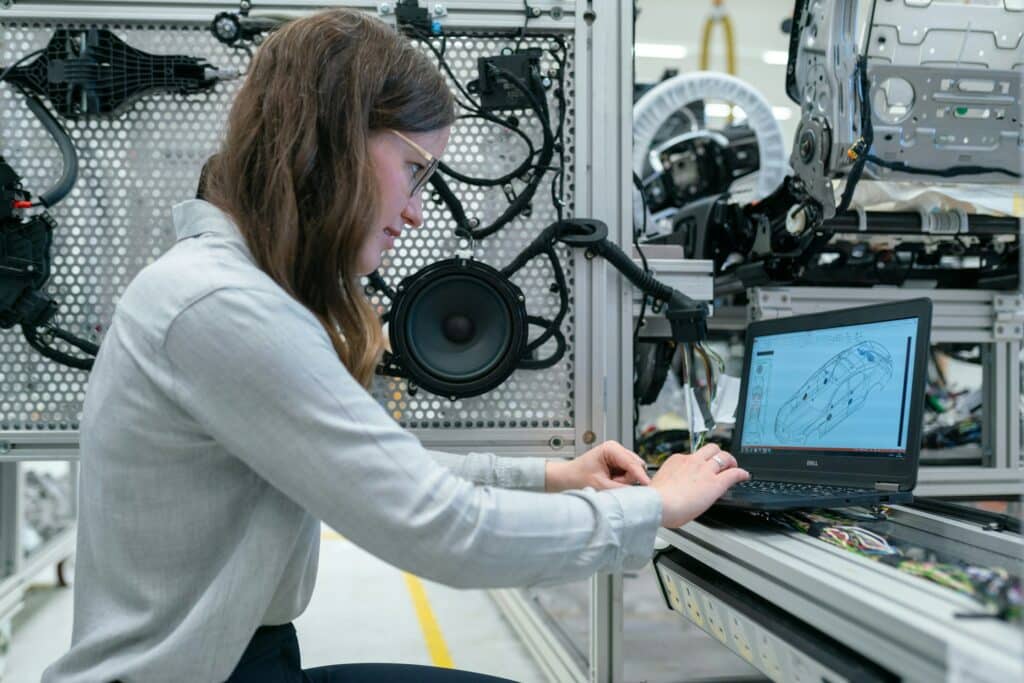
Modern manufacturing businesses increasingly rely on technology to get things done, yet IT management is too often treated like a secondary priority, if it is even counted at all. Think of how many different systems, databases and connections you have embedded within your processes right now – what would happen to your supply or distribution chain if any one of them broke down right now, and would you still be able to turn a profit if several of them stopped working at the same time?
This article will explore the top IT challenges faced by manufacturers, and some of the best solutions to help solve them:
IT Challenges in Manufacturing
Manufacturing environments live with a two-pronged cybersecurity pain point – protecting both back-office and production-related systems. This includes multiple assets, networks, software applications and integrations with external solutions that partners or customers use for connected processes (EDI, shipping, etc.), all needing monitoring, maintenance and often optimization to function as intended.
This is just one example of the unique IT headaches manufacturers face, and the others are no less challenging:
- Multiple business platforms in play requiring seamless integration
- Real-time data needed for ongoing processes
- Regulatory compliance specific to manufacturing and distribution
- Vulnerabilities in operational technology and industrial control systems
- Legacy systems performing alongside modern software
Addressing these and other factors requires a certain level of expertise as well as patience and vigilance. This is why many businesses will often turn to a managed service provider (MSP) to outsource their critical IT management and troubleshooting needs; however, choosing the right MSP in manufacturing means finding a partner that understands the unique pain points in your industry.
Regulatory Compliance
Manufacturers are always navigating a complex regulatory landscape that includes general and industry-specific requirements, from NIST frameworks to FDA and ISO certifications. Compliance demands intricate knowledge of where these come into play throughout the supply chain, and dedicating time and resources to enforcing it throughout.
Nonconformance with these various regulations – as well as customer expectations – risk a range of penalties and damages, including loss of contracts, fines and reputational damages. Technology ecosystems introduce their own opportunities and challenges for this arena, necessitating more proactive work to scale one and avoid the other.
Data Security
Even without a regulatory obligation, data is a valuable and often highly sensitive commodity that manufacturers must make efforts to protect. Hackers can do a lot of damage with the right access, escalating from gaining entry into your network in the first place to selling off your proprietary information or just holding it hostage for a ransom.
Security incidents in manufacturing environments can also have other immediate consequences beyond data loss and ransomware extortion, including production downtime, physical equipment damage and supply chain disruptions. The integration of operational technology with information systems creates potential gaps and additional cybersecurity complexities that must be monitored as well.
Disconnected Technology Stacks
Manufacturers typically rely on multiple software systems, including ERP (Enterprise Resource Planning), MES (Manufacturing Execution Systems), SCADA (Supervisory Control and Data Acquisition) and PLM (Product Lifecycle Management). As Industry 4.0 also continues to grow in adoption, this will mean increased proliferation of remote, sensor-based connections throughout shop and factory floors, adding even more applications to your IT stack.
A varied and disconnected software collection can present its own IT challenges, though having a streamlined and seamlessly integrated ecosystem will also provide you with opportunities to accelerate processes. The key is to have proactive management in place that gets ahead of security gaps and optimizes performance.
Shadow IT Ecosystem
When official IT resources cannot meet immediate operational needs, employees will often turn to unauthorized systems that create a “shadow IT” ecosystem. Hidden devices and applications not tracked by your network administrators can create security vulnerabilities, compliance issues and maintenance problems while undermining your technology governance.
Shadow IT networks typically emerge from a combination of lack of resources or capabilities in existing assets, and the ready availability of external systems or tools that can help an employee scale their productivity more immediately. The historically piecemeal transition from legacy technologies to newer solutions in manufacturing unfortunately creates a tempting gap for many to fill in with personal devices or third-party apps, which can go unnoticed until some enterprising hacker takes advantage of the hidden endpoint to breach your network.
Distributed Networks
Between leveraging multiple software and hardware systems as well as connections between various locations or channels, many manufacturers often host a variety of digital networks within their ecosystem. This could also introduce additional cybersecurity and operational challenges for your IT infrastructure, increasing the risk of something going wrong and impacting your business.
As new technologies like IoT or cloud-based and AI-powered systems add in even more remote connections and endpoints, maintaining network security and reliability become even greater priorities in a manufacturing environment. Between protecting your entire potential attack surface and guaranteeing uptime for each node consistently, this area of IT management becomes its own full time job.
IT Solutions for Manufacturing Challenges
Manufacturers need robust solutions to address these diverse technology challenges. While each environment has unique requirements, several core IT approaches can significantly reduce risks while reducing the burden on your internal teams:
Compliance as a Service (CaaS)
Working with compliance specialists means you do not have to become an expert in every regulation affecting your business. Instead, you can focus on your manufacturing operations while your MSP provides guidance on the constantly changing landscape of requirements and documentation.
Compliance as a Service (CaaS) often includes, but is not limited to:
- Regular compliance assessments against relevant frameworks
- Documentation management and maintenance
- Control implementation guidance and verification
- Remediation planning for identified gaps
Network Monitoring & Management
Good network management does not wait for things to break – it helps prevent issues before they impact your operations. The right IT provider will be one that understands that in manufacturing, every minute of unplanned downtime directly affects your bottom line.
Effective network management for manufacturing environments includes:
- Performance optimization for various applications
- Rapid response protocols for critical systems
- Monitoring across your entire connected ecosystem
- Maintenance that works around your production schedule
Permission & Access Management
Permission-based controls help you manage who has access to what in your IT ecosystem, reducing the risk of both external and internal threats without creating unnecessary obstacles for employees who need to get their jobs done.
Effective access management strategies for manufacturers include:
- Role-based access controls aligned with job functions
- Secure authentication methods for software environments
- Automated user provisioning and deprovisioning
- Regular access reviews and privilege adjustments
Backup & Recovery Solutions
A good business continuity strategy is not just about making copies of files – it must ensure you can get critical systems back online quickly when problems occur. This means testing your backups regularly and making sure your recovery approach aligns with how your business actually operates.
A comprehensive backup strategy protects manufacturing continuity by:
- Securing system configurations for rapid restoration
- Enabling fast recovery from ransomware attacks
- Maintaining ERP and other business system continuity
- Supporting compliance with data retention requirements
Co-Managed IT Services
Co-managed services work alongside your existing IT staff rather than replacing them. This approach augments your internal team, empowering them to continue leveraging their valuable knowledge about your specific environment while providing additional resources and specialized expertise where needed.
For manufacturing organizations, co-managed IT provides:
- Scalable resources for project implementation
- Access to enterprise-grade security and monitoring tools
- Strategic technology planning and roadmapping
- Support for both operational and business systems
- Additional expertise when you need it
MSP for Manufacturing
Finding a provider who understands your industry means having a partner that will recognize the difference between a minor issue and something that could shut down your production line. Your MSP should have experience with industrial systems, production software and the regulatory environment specific to your manufacturing sector. When evaluating potential IT service providers, consider whether they offer:
- Experience supporting ERP, MES, etc.
- Understanding of industrial network requirements
- Knowledge of manufacturing compliance frameworks
- Expertise in handling operational and information technology integrations
- Capability to support 24/7 operations
SWK Technologies has been recognized by industry analysts for our expertise in the manufacturing sector, earning a place on ChannelE2E’s Top 100 Vertical Market MSPs list specifically for this industry. This recognition reflects our deep understanding of the unique technology challenges manufacturers face and our commitment to providing solutions that address those specific needs.
Work with an Award-Winning MSP in Manufacturing
Technology disruptions in manufacturing environments directly affect your bottom line through production delays, quality issues and supply chain interruptions. By addressing these critical IT challenges proactively, your manufacturing business can minimize technology-related risks while maximizing operational efficiency.
Contact SWK Technologies here to see how our IT solutions can strengthen your technology infrastructure and support your business success.
